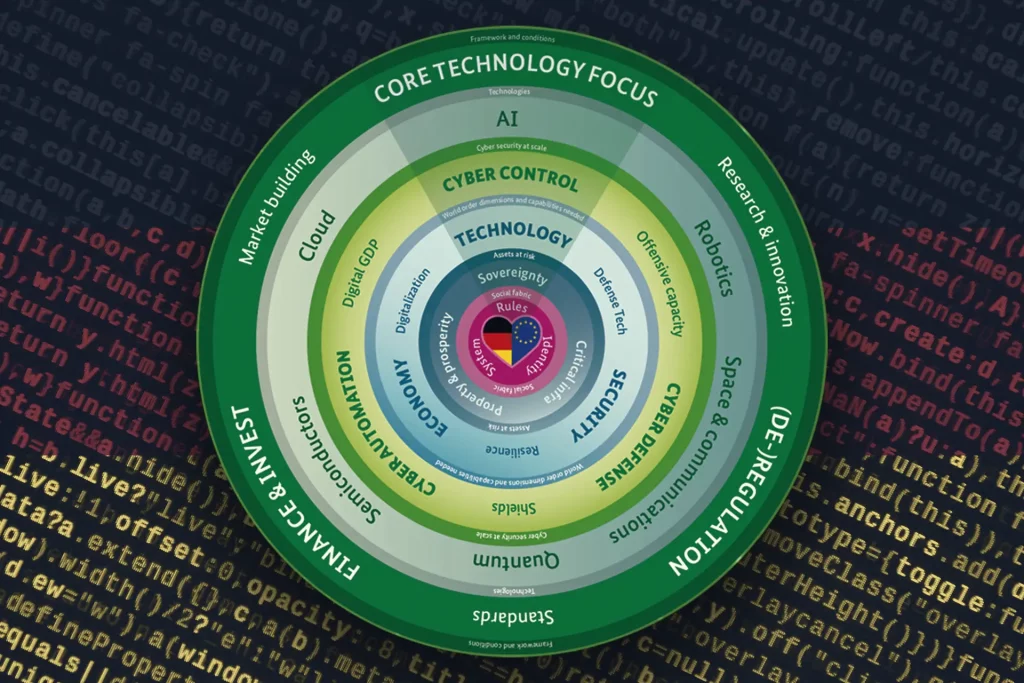
The cybersecurity budget adjustments currently are less about “more money” and more about reallocating spend away from a pure backup mindset toward prevention, identity, and data controls—accelerated by AI risks and geopolitical tensions.
Cybersecurity budget adjustments are shifting toward prevention
When it comes to cybersecurity budget adjustments for 2026, a clear turning point is emerging. CFOs are approving higher budgets in many organizations, but they also want to allocate those funds differently. The rationale is straightforwardly financial. Modern extortion increasingly relies on data theft, reputational pressure, and regulatory “tail costs,” rather than only on encrypted systems that can be restored from backups. As a result, the guiding question in budget meetings is shifting from “How quickly can we recover?” to “How do we prevent the damage from happening in the first place—and from dragging on for months?”
This shift is well captured in a line that CFO Brew translates directly into budget logic. Cyber insurers are advising CFOs to move investment “from backup to prevention” because the “crime economy” is shifting toward reputational leverage through stolen data. This is not an attack on backups; it highlights a gap in thinking, since even a flawless restore does not stop the publication of sensitive data, a wave of lawsuits, or a loss of trust.
Why cybersecurity budget adjustments are increasingly CFO-led
At the same time, pressure is rising from a second angle. In finance circles, cybersecurity is increasingly treated as a balance-sheet and disclosure-relevant risk, especially when geopolitical conflicts increase the likelihood of attacks against banks, enterprises, and their service providers. In this context, Fortune quotes a CFO voice emphasizing timing. Amid annual planning and insurance renewals, this is the critical window to reassess vendor resilience and coverage gaps, and cybersecurity is “must-have” explicitly alongside AI investments. For cybersecurity budget adjustments, that means it’s not just about tools. It also includes defensible evidence, exercises, supply-chain playbooks, and the decision of which risks the organization deliberately retains. You can also see a long-awaited increase in awareness of topics typically addressed by business continuity management systems.
The CFO perspective also changes the evaluation criteria. Prevention is no longer justified by feature lists but by loss categories such as data exfiltration, fraud, downtime, contractual penalties, fines, litigation costs, and reputational damage. Every investment must either reduce the likelihood of an incident or cap the maximum loss—and both must be measurable.
AI is reshaping the attack surface and driving cybersecurity budget adjustments
AI changes security needs in very concrete ways. AI systems are embedded in workflows, automatically access data sources, and rely on API keys, tokens, and machine identities to do so. That raises the importance of identity governance and data controls. The Thales blog on the 2026 Data Threat Report describes AI as a “trusted insider” because AI tools often receive broad access, sometimes with less control and oversight than human users. The takeaway is easy for budget owners to translate. If access rights, secrets handling, and information classification are weak, AI scales those weaknesses at high speed.
Sixty-one percent of surveyed organizations cite AI as the top risk to data security, and 70 percent say the pace of AI-driven transformation is the biggest security challenge. At the same time, foundational gaps become visible that many AI programs underestimate. Only 34 percent reportedly know where all their data resides, 39 percent can fully classify it, and 47 percent of sensitive cloud data remains unencrypted. Anyone pushing AI into production workflows must therefore budget in parallel for data visibility, classification, encryption, and access governance. Otherwise, value may grow—but risk grows faster.
AI also shifts the loss profile toward fraud and brand impact. The Thales piece reports nearly 60 percent experiencing deepfake-driven attacks and 48 percent reporting reputational harm from AI-generated disinformation. That pulls traditional finance processes into the scope of cybersecurity budget adjustments. Payment approvals, supplier communications, and executive communications become attack surfaces that require technical and procedural hardening.
Resilience becomes ongoing operations, not just an incident project
Alongside data security, availability is moving back to the forefront. DDoS and application-layer attacks look less like rare outliers and more like sustained load. A current example from Europe illustrates this. The European Cyber Report 2026 from Link11 states that the longest observed attack lasted 12,388 minutes and that attacks in 2025 were active 88 percent of the time, equivalent to 322 days per year. It also reports a 75 percent increase in documented attacks in 2025 following a 137 percent increase the year before.
The financial conclusion is uncomfortable but clear. Resilience must be planned as an always-on capability. Controls that are only ramped up once an attack is underway do not fit attack patterns optimized for endurance, repetition, and variation.
How cybersecurity budget adjustments can be structured in practice
Identities should sit at the center, because tokens, API keys, and machine accounts in AI and cloud environments are the fastest route to data. Data governance needs an upgrade, because classification and encryption are not just compliance. They are prerequisites for using AI in a controlled way. Detection and response must be tuned for exfiltration and fraud, not only for encryption events. Availability should be treated as a business continuity capability, including regular failover and recovery testing.
Another major block concerns service providers. Vendor and supply-chain risks should be treated as material enterprise risks. That requires budget for assessments, contractual minimum standards, and playbooks that support incident response across organizational boundaries. It may be less glamorous than buying a new tool, but it improves evidence readiness, insurability, and response speed.