Trump’s cyber strategy puts U.S. cyber policy on a tougher footing. On March 6, 2026, the White House published the new strategy and an accompanying Executive Order targeting cybercrime, fraud, and scam operations. At the center are more offensive cyber operations, greater private-sector involvement, the protection of critical infrastructure, and more direct government action against transnational cybercrime networks; early media reactions describe this as a clear policy shift, while also pointing to the brevity of the paper and the fact that implementation is still pending.
Trump’s cyber strategy puts the United States on a tougher course
The U.S. government published its new cyber strategy on March 6, significantly hardening the national security tone in the digital domain. The seven-page policy paper sets out an ambition that goes beyond traditional network defense: the United States wants to address threats earlier, degrade adversary capabilities, and explicitly use the full range of defensive and offensive cyber operations, law enforcement, diplomacy, and economic pressure. At the same time, the White House issued an Executive Order on cybercrime, fraud, and predatory schemes, immediately backing the political direction with concrete deadlines.
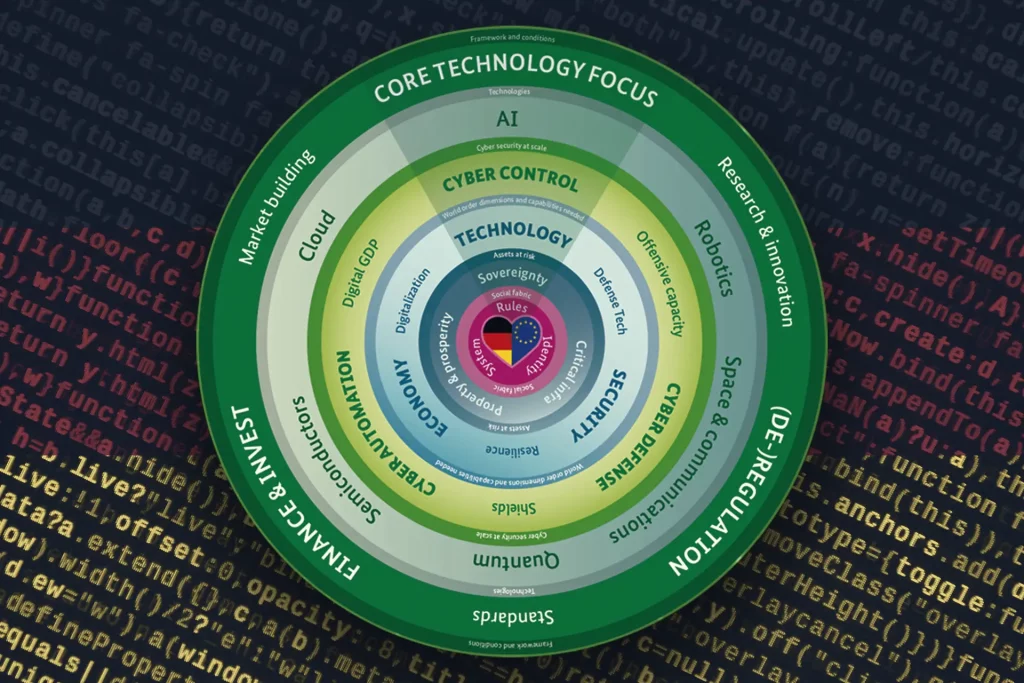
In substance, the administration organizes Trump’s cyber strategy around six pillars. These include shaping adversary behavior, what the administration describes as “common-sense” regulation, modernizing and securing federal networks, protecting critical infrastructure, achieving technological superiority in AI and quantum technologies, and building talent and capacity. The strategy therefore does not focus on individual products or software versions, but on broad segments of U.S. digital policy: federal agencies, critical infrastructure operators, supply chains, data centers, telecommunications, energy, water, financial systems, and hospitals.
What Trump’s cyber strategy specifically provides for
The tone is especially clear in its treatment of adversaries and cybercriminals. The strategy states that the United States will not wait to fight threats inside its own networks, but will seek to disrupt hostile campaigns before they successfully penetrate them. To do so, Washington says it will use the “full range” of offensive and defensive cyber capabilities. At the same time, the private sector is expected to play a larger role. Companies are to be incentivized to identify hostile infrastructure and help disrupt it. In that sense, the administration moves further away from a purely defensive understanding of state cyber policy and places greater emphasis on deterrence, disruption, and increasing costs for attackers.
A second focus lies on critical infrastructure and federal networks. Trump’s cyber strategy explicitly mentions zero-trust architectures, cloud modernization, post-quantum cryptography, and the broader use of AI-supported security solutions. In the area of critical infrastructure, the emphasis is on hardening systems, speeding recovery after incidents, and reducing dependencies on technologies viewed as adversarial. The strategy also refers to secure supply chains, protecting data centers, and safeguarding AI technology stacks. Cyber policy is thus framed not only as a defense issue, but also as an industrial, technological, and competitiveness issue.
Also new is the explicit link to everyday online crime. The strategy and the accompanying order treat ransomware, phishing, financial fraud, sextortion, and identity abuse not as side issues, but as core national security problems. The White House argues this point on the basis of the economic and social damage involved. Among the supporting data are FTC figures showing that U.S. consumers reported more than $12.5 billion in fraud losses in 2024. Trump’s cyber strategy ties that finding to a tougher line against transnational criminal groups and against states that tolerate or fail to effectively combat such operations.
The Executive Order immediately reinforces the new course
The new direction becomes operationally tangible above all through the Executive Order. It requires a review of existing operational, technical, diplomatic, and regulatory tools within 60 days. Within 90 days, the Attorney General is to submit a recommendation for a Victims Restoration Program, meaning a mechanism through which seized funds could be returned to victims of cyber-enabled fraud. Within 120 days, an action plan must follow that identifies the responsible transnational groups and bundles proposals for prevention, disruption, investigation, and dismantling these structures. Starting from March 6, 2026, the first milestones therefore fall on May 5, June 4, and July 4, 2026.
There is also an institutional component: within the National Coordination Center, an operational cell is to coordinate federal measures and explicitly integrate intelligence, technical capabilities, and threat data from the private sector. This matters in practice because, alongside law enforcement, the order also provides for training and resilience measures for states, municipalities, as well as tribal and territorial authorities. The foreign policy lever is also clearly defined. The State Department is to pressure foreign governments if they tolerate scam centers or other cybercriminal structures on their territory. As possible consequences, the order lists sanctions, visa restrictions, trade measures, aid cuts, and, in certain cases, the expulsion of involved officials.
Initial reactions remain cautious
In the initial response, the move is being read primarily as a hardening of the political course, rather than as a fully developed implementation program. Bloomberg Law highlights the more offensive tone, the stronger role of AI, and the stated intention to further “unleash” the private sector. Axios, by contrast, places more emphasis on the brevity of the document, the still-pending implementation plan, and the difficult situation facing CISA in the background. Trade outlets such as Nextgov/FCW and Cybersecurity Dive assess the strategy in similar terms: clear in its political signal, but thin on detail.
Critical voices so far also focus more on implementation than on rejecting the strategy outright. At the Institute for Security and Technology, observers point to continuity with earlier strategies, while also stressing that without a credible implementation plan it will be difficult to measure whether the sharper tone actually leads to greater security. They also note that offensive disruption alone does not eliminate the structural causes behind many cyber incidents, such as insecure software, known vulnerabilities, or outdated systems.
For now, Trump’s cyber strategy therefore marks above all a political recalibration. The emphasis is shifting visibly away from pure defense toward a broader concept built around deterrence, technological dominance, stronger industry involvement, and more direct action against cyber-enabled crime. Whether this becomes more than a tough statement of principle will become clear in May, June, and July. By then at the latest, the U.S. government will have to show how it intends to translate its more offensive ambition into agency practice, cooperation with the private sector, and concrete measures against cybercrime